CSRF is when a user is tricked into executing functions on a webpage without their knowledge. This can be via a crafted link with the actions performed when the user clicks it or via stored XSS so it executes when a user browses the page.
How is this possible?
CSRF is only possible when there are no anti-csrf tokens present or any other way to validate a users identity. There is no way for the web application to know that you intended to perform those actions or not. The web application just sees the request from you and executes the request as per normal. This means that anyone can send you a link or direct you to a none related web page with the attack in the source code and the web application will execute the command on your behalf. Often times without any indication of what has just happened.
Example:
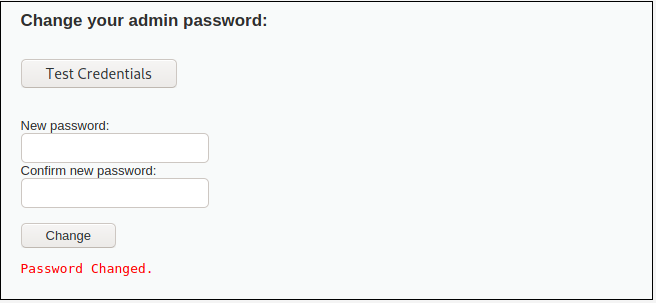
Take a password reset form:
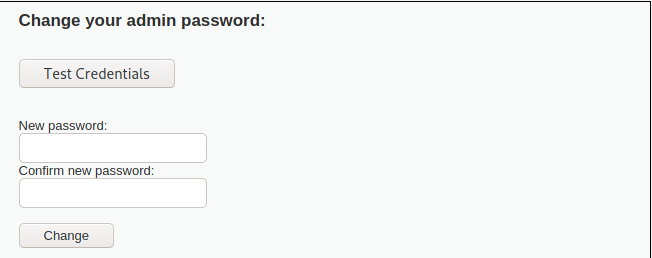
When the “Change” button is clicked, this link is generated and executed by the web application:
http://192.168.1.50/dvwa/vulnerabilities/csrf/?password_new=password123&password_conf=password123&Change=Change
So what is stopping an attacker sending this link to someone currently logged into the website and changing their password? Or embedding this link in a stored XSS?
Creating a link like this and clicking it will result in my password being changed to “my_new_password“
http://192.168.1.50/dvwa/vulnerabilities/csrf/?password_new=my_new_password&password_conf=my_new_password&Change=Change
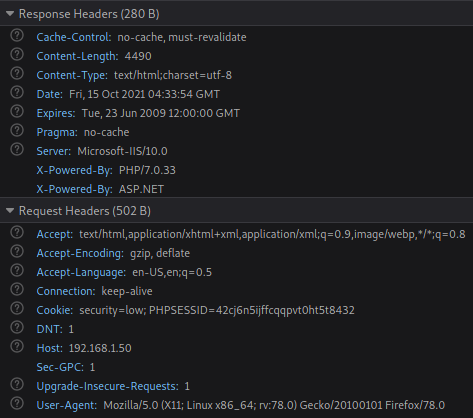
Looking at the Request and Response headers we can confirm there are no CSRF tokens which would prevent this attack.
Mitigation
Configure CSRF tokens on the web application. A CSRF token is a random string that is sent to the user in the first response from the web application. The web server keeps track of this token and ensures it is present in every subsequent request from the user. Thus, if there is no token present the web application will not execute the users request. Another layer of protection against csrf is requiring users enter their current password before changing to a new one.